Netflow is the protocol developed by Cisco to manage data about IP traffic. In a few words using Netflow you can collect data about all IP data send/received on multiple Cisco/Linux/BSD/Juniper hosts and send it to central Netflow collector that will show you the nice graphs and also will allow to have a complete picture of what data was sent/received on those hosts (including destination and source IP, port, bytes transfered, int/out interfaces etc). Nfdump is netflow collector. Nfsen is graphical tools for generating graphs and querying Nfdump for historical traffic reports. In this article you will see how to deploy all this staff in Linux.
Netflow probe is required to collect IP traffic data on Linux host. In general this piece of sofware will sit in background, store every network activity on certain network interface and then send collected data to Netflow collector nfdump. As Netflow probe I prefer fprobe that is totally simple application that just does its job. If you feel that fprobe is not what you need or there are some problems with installing it you can try softflowd that can do the same job.
Install fprobe from sources:
cd /usr/src/ sudo -s wget https://sourceforge.net/projects/fprobe/files/fprobe/1.1/fprobe-1.1.tar.bz2/download tar -xvjf fprobe-1.1.tar.bz2 cd fprobe-1.1 ./configure --prefix=/ make make install
Point fprobe to one of network interfaces of Linux host and make it to send data to Netflow collector:
fprobe -i eth0 11.22.33.44:23456
In above example fprobe stores all data trasnfers on eth0 network interface and sends collected data to 11.22.33.44 host via 23456 UDP port (you may want to change firewall rules to make Netflow working over 23456 UDP port).
Install nfdump Netflow collector from sources:
cd /usr/src/ sudo -s wget https://sourceforge.net/projects/nfdump/files/stable/nfdump-1.6.2/nfdump-1.6.2.tar.gz/download tar -xvzf nfdump-1.6.2.tar.gz cd nfdump-1.6.2 ./configure --prefix=/ --enable-nfprofile make make install
When finished Netflow collector becomes ready so you can start capturing traffic from Netflow probe. If you don’t need any graphical tools like nfsen described below you can just start collector and save Netflow data in /var/neflow/ directory (THIS STEP IS OPTIONAL):
/bin/nfcapd -w -D -p 23456 -B 200000 -S 1 -z -I Linux-Host-1-eth0 -l /var/netflow/
In order to install nfsen from sources you have to get all its prerequisites, run one of below lines depending on what Linux distro you’re using (1st line is for Fedora, Centos, Redhat while 2nd line is for Ubuntu, Debian, Mint and similar):
yum install rrdtool rrdtool-devel rrdutils perl-rrdtool -y
or
aptitude install rrdtool librrd2-dev librrd-dev librrd4 librrds-perl librrdp-perl
Compile nfsen from sources:
cd /usr/src/ sudo -s wget https://sourceforge.net/projects/nfsen/files/stable/nfsen-1.3.5/nfsen-1.3.5.tar.gz/download tar -xvzf nfsen-1.3.5.tar.gz cd nfsen-1.3.5 cp etc/nfsen-dist.conf etc/nfsen.conf
In order to continue the installation you should edit file etc/nfsen.conf to specify where to install nfsen, web server’s username (yes, you have to install apache, lighttpd, nginx or any other web server first), its document root directory etc. The major section of that config file is ‘Netflow sources’ that must list all hosts you’ve started Netflow probes at. Here is an example section for monitoring above Linux host:
%sources = (
'Linux-Host-eth0' => { 'port' => '23456', 'col' => '#ff0000', 'type' => 'netflow' },
);
When finished it’s time to actually install nfsen using installation script:
./install.pl etc/nfsen.conf
In case of successful installation you will be notified with corresponding congratulations message so it would be proper time to start nfsen daemon:
/path/to/nfsen/bin/nfsen start
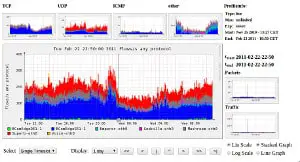
Now you can open http://localhost/nfsen/nfsen.php at Linux host where nfsen was installed to start using this Netflow tool and see some graphs. Notice that it takes about 5-10 minutes to see first bars at the graphs, if the graphs are still empty you will have to check at least the following:
1. If fprobe is able to communicate to Netwflow collector and can send Netflow data to it (use ‘ps ax | grep fprobe’ and Linux host being monitored and tcpdump tool at Netflow collector).
2. If Netflow collector is started and can receive data from Netflow probe. Use ‘ps ax | grep nfcapd’ and tcpdump at Netflow collector Linux host.
If you can add anything — feel free to drop a comment below.

Many thanks for the extremely useful article, really solved my problems.
Although as it is the first time that I’m using tools like that i have some question and i will be really glad if someone can answer them:
1) Nfsen contains flows and diagrams so i’m almost sure that fproble and nfdump works. Although when i’m going to the folder data/nfsen/profiles-data/live/myrouter/… there are many file like nfcapd.201307201235 and a lot of them are empty (nfdump -r /data/nfsen/profiles-data/live/MYROUTER/2013/07/20/nfcapd.201307201235) so i guess there is something wrong with the command or timeouts. What i can do to fix that?
2) /data/nfsen/profiles-data/live/MYROUTER… is the folder where flows suposed to be saved or there is another folder where nfdump save the flows?
3)until now the files that contains flows have those fields: date flow start, duration, protocol, scr ip : port, dst ip: port, packets, bytes, flows. Although i would like to capture more information that netflow supports like TCP flags. Can someone tell me how to construct my command to capture more info?
Answered question 3 by my self 🙂 so let me add one more question, how can i export the nfcapd flows to mysql?